The modern business world is increasingly interconnected as vast amounts of personal data, and access to this data, are shared with third parties for business efficiency.
Although this makes many business processes easier and cost-efficient, it also increases the risks arising from the involvement of third parties. For instance, Fullerton Health suffered a data breach as a result of a hack of their vendor's server in October 2021.
Despite good intentions to provide useful products and services, data breaches can happen to any organisation, in any industry, as long as they collect, use and share any form of personal data. Hence, knowing how to do the necessary due diligence in appointing and managing a third-party vendor is vital for your organisation’s data protection posture.
A recent victim of a third-party data breach was Singtel, which had a third-party file-sharing system hacked in December 2020. The telco called the incident a "sophisticated cyberattack which included exploiting a previously unknown vulnerability.”
Another example of a third-party data breach took place in Malaysia, where a e-wallet service provider, Kiplepay, suffered a data breach involving its payment gateway vendor in Aug 2022. The company called the case a “recent potential third-party data breach incident” and investigations are ongoing.
To effectively manage third-party vendor risk and performance, it is imperative to have the necessary knowledge and expertise in this area. Key personnel in organisations can get hands-on in learning about third-party management through a simulated due diligence exercise in our course here.
Common mistakes when dealing with third parties
Most organisations make the following mistakes in the effort to procure a credible third-party vendor for outsourced services. These mistakes can be costly to the company in terms of financial losses, time and, in some cases, sustaining reputational damage and loss of revenue due to a breach.
Some errors made include:
- • A sole focus on price when choosing suppliers
- • Qualifying suppliers based on previous relationships
- • The failure to recognise the risks that third parties pose to the organisation
- • Assuming that large or established vendors pose a lesser risk
- • Insufficient contractual arrangements and protection
- • Lack of agreed performance indicators with suppliers or failure to monitor performance
- • Failure to audit, cultivate and sustain supplier relationships
- • Failure to track or respond to disputes, expiry, termination and renewals

Data and third-party vendor management
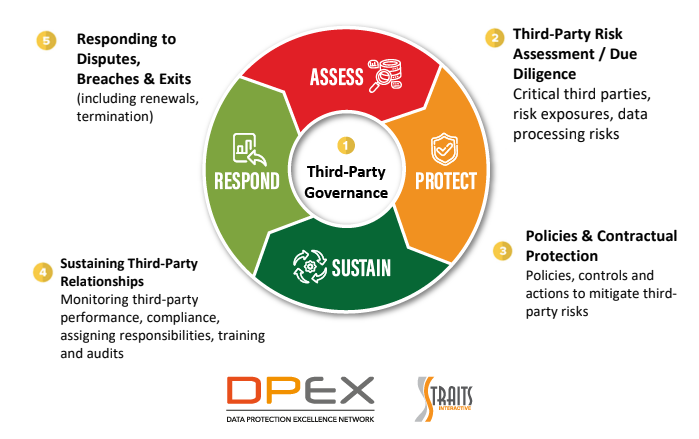
As part of effective third-party management, companies who work with third parties would evaluate the performance and risk posed by each vendor. In data protection, organisations would look at a framework called APSR (Assess, Protect, Sustain and Respond) when managing data protection activities, risks, and controls.
When handling third-party vendors, organisations can also choose to follow a similar approach as APSR. Throughout each stage of the framework, organisations need to be mindful of various factors before engaging a vendor.
- • Assess - Conducting the necessary third-party risk assessments (due diligence)
- • Protect - Ensuring that there are internal policies, controls, and actions to mitigate the third-party risks identified in the assessment stage
- • Sustain - Performing the essential activities to track the third-party vendor’s performance and compliance with the contract. Regular audits and staff training is also crucial.
- • Respond - Formulating a plan to respond to vendor disputes, breaches in contract or data breach, vendor exit process and vendor renewal process
With more stringent requirements based on the evolving regulatory environment, it is vital for organisations to establish effective third-party management governance. To do so, a third-party management plan should be formulated and aligned to the overall governance, risk management and compliance (GRC) strategy of the organisation.
Some factors to consider when developing the third-party management plan:
- • Ensure alignment of plan with the organisation’s overall GRC strategy
- • Selecting the right members to form the team in charge of third-party management
- • Risk mitigation strategies to pre-empt and address potential third-party risks throughout the third-party life cycle
For more Data Protection resources, visit www.dpexnetwork.org. Sign up for free as a member to have full access to all content. This article was first published on 17 December 2021.